!!!笔记仅供学习交流使用,请勿进行其他用途!!!
Nessus是一款非常强大的扫描和审计工具,这里只笔记下最简单的使用流程。kali下默认没有安装Nessus,因此这里需要手动下载和安装。
CONTENTS
下载和安装:
参考链接:
【 http://hi.baidu.com/huting/item/da97ec5314bd482933e0a9dc 】
【 http://uwnthesis.wordpress.com/2013/07/31/kali-how-to-install-nessus-on-kali/ 】
Nessus商用版本不是免费的,这里我们使用home版本来学习,下载地址:【 http://www.tenable.com/products/nessus/select-your-operating-system 】,这里作者下载的是:【 Nessus-5.2.6-debian6_amd64.deb 】
注册地址:【 http://www.tenable.com/products/nessus-home 】
安装和初始化方法:
root@kali:~# dpkg -i Nessus-5.2.6-debian6_amd64.deb Selecting previously unselected package nessus. (正在读取数据库 ... 系统当前共安装有 332892 个文件和目录。) 正在解压缩 nessus (从 Nessus-5.2.6-debian6_amd64.deb) ... 正在设置 nessus (5.2.6) ... nessusd (Nessus) 5.2.6 [build N25116] for Linux Copyright (C) 1998 - 2014 Tenable Network Security, Inc Processing the Nessus plugins... [##################################################] All plugins loaded - You can start nessusd by typing /etc/init.d/nessusd start - Then go to https://kali:8834/ to configure your scanner root@kali:~# /etc/init.d/nessusd start $Starting Nessus : .
然后使用浏览器打开【 https://127.0.0.1:8834/ 】,第一次进入后会提示输入用户名和密码,以及激活码,成功之后会下载最新的插件,初始化插件,会耗时一段时间。
这里笔记个地址,以后有机会学习下【 http://www.youtube.com/tenablesecurity 】
使用web版本:
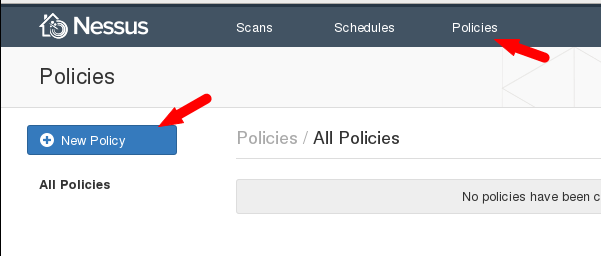
首先新建一个policy,如下图,这里有很多policy的模板,从这里也能看出Nessus是多么的强大~:
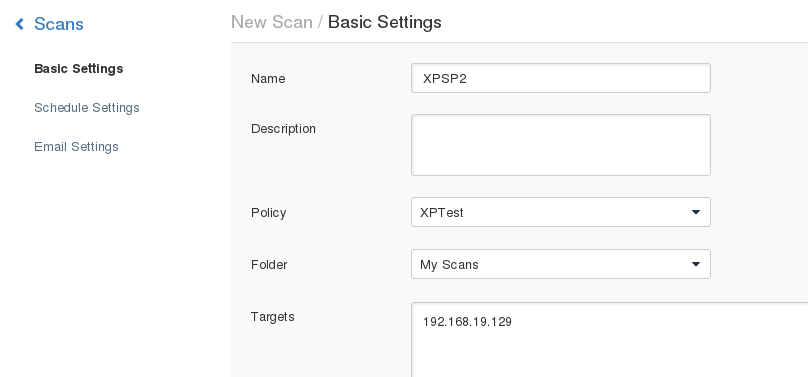
简单起见,这里以【 Basic Network Scan 】为模板,建立一个查找WinXP的漏洞的policy,取名为XPTest,【 scan type 】设置为【 external 】。
建立好之后,点击该policy进行修改,这里需要点击右边的【 Advanced Mode 】,如下图:

这里我们只使用最简单的Nessus扫描功能,扫描WinXP主机,因此,这里的plugins我们只启用3个,如下图:

建立好policy之后,我们新建一个scan任务,如下图,新建好之后就可以launch了。
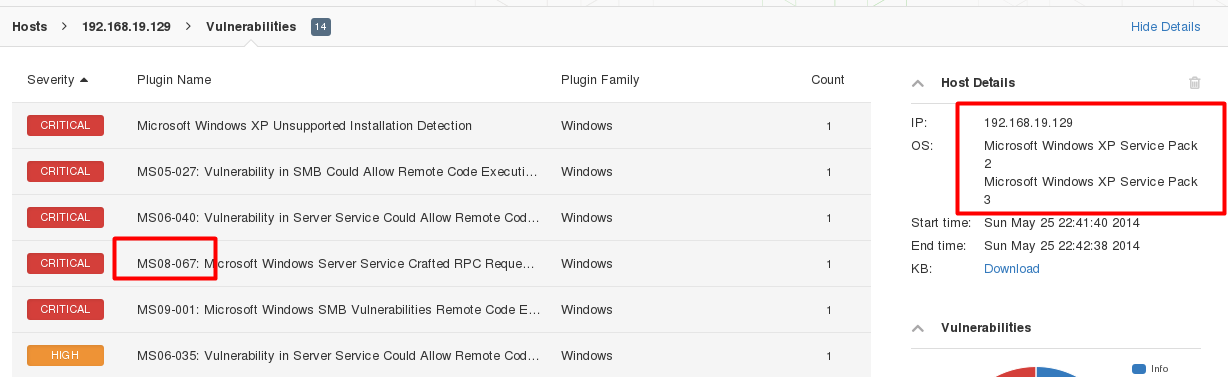
这里可以点击查看扫描结果,也可以查看详细的结果,如下图:

在Metasploit中使用:
和web版本的功能类似,但是功能有限,这里只笔记下最简单的使用命令:
root@kali:~# msfconsole
。。。。。
msf > load nessus #首先载入模块
[*] Nessus Bridge for Metasploit 1.1
[+] Type nessus_help for a command listing
[*] Successfully loaded plugin: nessus
msf > nessus_help #查看命令:
[*]
Command Help Text
------- ---------
Generic Commands
----------------- -----------------
nessus_connect Connect to a nessus server
nessus_save Save nessus login info between sessions
nessus_logout Logout from the nessus server
nessus_help Listing of available nessus commands
nessus_server_status Check the status of your Nessus Server
nessus_admin Checks if user is an admin
nessus_server_feed Nessus Feed Type
nessus_find_targets Try to find vulnerable targets from a report
nessus_server_prefs Display Server Prefs
Reports Commands
----------------- -----------------
nessus_report_list List all Nessus reports
nessus_report_get Import a report from the nessus server in Nessus v2 format
nessus_report_vulns Get list of vulns from a report
nessus_report_hosts Get list of hosts from a report
nessus_report_host_ports Get list of open ports from a host from a report
nessus_report_host_detail Detail from a report item on a host
Scan Commands
----------------- -----------------
nessus_scan_new Create new Nessus Scan
nessus_scan_status List all currently running Nessus scans
nessus_scan_pause Pause a Nessus Scan
nessus_scan_pause_all Pause all Nessus Scans
nessus_scan_stop Stop a Nessus Scan
nessus_scan_stop_all Stop all Nessus Scans
nessus_scan_resume Resume a Nessus Scan
nessus_scan_resume_all Resume all Nessus Scans
Plugin Commands
----------------- -----------------
nessus_plugin_list Displays each plugin family and the number of plugins
nessus_plugin_family List plugins in a family
nessus_plugin_details List details of a particular plugin
User Commands
----------------- -----------------
nessus_user_list Show Nessus Users
nessus_user_add Add a new Nessus User
nessus_user_del Delete a Nessus User
nessus_user_passwd Change Nessus Users Password
Policy Commands
----------------- -----------------
nessus_policy_list List all polciies
nessus_policy_del Delete a policy
msf > nessus_connect root:123456@127.0.0.1:8834 #登陆服务器
[*] Connecting to https://127.0.0.1:8834/ as root
[*] Authenticated
msf > nessus_save #保存session
[+] /root/.msf4/nessus.yaml created.
msf > nessus_policy_list #查看policy,这里没有新建policy的命令
[+] Nessus Policy List
[+]
ID Name Comments
-- ---- --------
1 XPTest
msf > nessus_report_list #查看所有的扫描记录
[+] Nessus Report List
[+]
ID Name Status Date
-- ---- ------ ----
0577dd54-0fa8-7197-ef66-20a5e1fbcc865dcaa6cd19cef8d0 XPSP2 completed 22:42 May 25 2014
[*] You can:
[*] Get a list of hosts from the report: nessus_report_hosts <report id>
msf > nessus_report_vulns 0577dd54-0fa8-7197-ef66-20a5e1fbcc865dcaa6cd19cef8d0 #查看某个记录
[*] Grabbing all vulns for report 0577dd54-0fa8-7197-ef66-20a5e1fbcc865dcaa6cd19cef8d0
[+] Report Info
Hostname Port Proto Sev PluginID Plugin Name
-------- ---- ----- --- -------- -----------
。。。。。。
。。。。。。
msf > nessus_scan_new #新建一个scan的命令
[*] Usage:
[*] nessus_scan_new <policy id> <scan name> <targets>
[*] use nessus_policy_list to list all available policies
发表评论