!!!笔记仅供学习交流使用,请勿进行其他用途!!!
CONTENTS
官方提供的下载方式:
w3af_console的使用:
w3af_console的使用方式和metasploit类似,这里简单的列下可用的各级菜单:
root@kali:~# w3af_console #启动w3af控制台 w3af>>> help #显示w3af的命令,和metasploit的使用方式类似 |-------------------------------------------------------------------| | start | Start the scan. | | plugins | Enable and configure plugins. | | exploit | Exploit the vulnerability. | | profiles | List and use scan profiles. | | cleanup | Cleanup before starting a new scan. | |---------------------------------------------------------------| | help | Display help. Issuing: help [command] , prints more specific help about "command" | | version | Show w3af version information. | | keys | Display key shortcuts. | |----------------------------------------------------------| | http-settings | Configure the HTTP settings of the framework. | | misc-settings | Configure w3af misc settings. | | target | Configure the target URL. | |---------------------------------------| | back | Go to the previous menu. | | exit | Exit w3af. | |---------------------------------------------------------| | kb | Browse the vulnerabilities stored in the Knowledge Base | |-------------------------------------------------| w3af>>> plugins #plugins菜单 w3af/plugins>>> help |-------------------------------------------------| | list | List available plugins. | |-------------------------------------------------| | back | Go to the previous menu. | | exit | Exit w3af. | |-------------------------------------------------| | infrastructure | View, configure and enable infrastructure plugins | | mangle | View, configure and enable mangle plugins | | crawl | View, configure and enable crawl plugins | | bruteforce | View, configure and enable bruteforce plugins | | grep | View, configure and enable grep plugins | | evasion | View, configure and enable evasion plugins | | audit | View, configure and enable audit plugins | | auth | View, configure and enable auth plugins | | output | View, configure and enable output plugins | |-------------------------------------------------| w3af/plugins>>> list audit #查看audit模块 |------------------------------------------------| | Plugin name | Status | Conf | Description | |------------------------------------------------| 。。。。。 。。。。。 | xst | | | Find Cross Site Tracing vulnerabilities. | |------------------------------------------------| w3af>>> exploit #exploit菜单 w3af/exploit>>> help |-------------------------------------------------| | list | List available exploits. | | exploit | Exploit a vulnerability found by audit plugins. | | interact | List and interact with shell objects generated by exploit plugins. | |-------------------------------------------------| | back | Go to the previous menu. | | exit | Exit w3af. | |-------------------------------------------------| w3af/exploit>>> list #显示可用的exploit工具 |-------------------------------------------------| | Plugin | Description | |-------------------------------------------------| | sqlmap | Exploit web servers that have sql injection vulnerabilities using sqlmap. | | file_upload | Exploit applications that allow unrestricted file uploads inside the webroot. | | xpath | Exploit XPATH injections with the objective of retrieving the complete XML text. | | local_file_reader | Exploit local file inclusion bugs. | | os_commanding | Exploit OS Commanding vulnerabilities. | | dav | Exploit web servers that have unauthenticated DAV access. | | eval | Exploit eval() vulnerabilities. | | rfi | Exploit remote file include vulnerabilities. | |-------------------------------------------------| w3af>>> profiles #配置菜单 w3af/profiles>>> help |-------------------------------------------------| | use | Use a profile. | | list | List available profiles. | | save_as | Save the current configuration to a profile. | |-------------------------------------------------| | back | Go to the previous menu. | | exit | Exit w3af. | |-------------------------------------------------| w3af/profiles>>> list #显示可用的攻击配置 |-------------------------------------------------| | Profile | Description | |-------------------------------------------------| | bruteforce | Bruteforce form or basic authentication access controls using default credentials. To run this profile, set | | | the target URL to the resource where the access control is, and then click on Start. | | audit_high_risk | Perform a scan to only identify the vulnerabilities with higher risk, like SQL Injection, OS Commanding, | | | Insecure File Uploads, etc. | | full_audit_manual_disc | Perform a manual discovery using the spiderMan plugin, and afterwards scan the site for any known | | | vulnerabilities. | | full_audit | This profile performs a full audit of the target website, using only the webSpider plugin for discovery. | | OWASP_TOP10 | The Open Web Application Security Project (OWASP) is a worldwide free and open community focused on improving | | | the security of application software. OWASP searched for and published the ten most common security flaws. | | | This profile search for this top 10 security flaws. For more information about the security flaws: | | | http://www.owasp.org/index.php/OWASP_Top_Ten_Project . | | fast_scan | Perform a fast scan of the target site, using only a few discovery plugins and the fastest audit plugins. | | empty_profile | This is an empty profile that you can use to start a new configuration from. | | web_infrastructure | Use all the available techniques in w3af to fingerprint the remote Web infrastructure. | | sitemap | Use different online techniques to create a fast sitemap of the target web application. This plugin will only | | | work if you've got Internet access and the target web application is being spidered by Yahoo! | |-------------------------------------------------| w3af>>> keys #各种快捷键 |-------------------------------------------------| | Ctrl-A / Ctrl-E | Move cursor to the beginning/end of the line. | | Ctrl-H | Erase the character before the cursor. | | Ctrl-W | Erase the word before the cursor. | | Ctrl-L | Clear screen. | | Ctrl-D, Ctrl-C | Return to the previous menu or exit w3af. | |-------------------------------------------------| w3af>>> target #目标菜单 w3af/config:target>>> help |-------------------------------------------------| | view | List the available options and their values. | | set | Set a parameter value. | | save | Save the configured settings. | |-------------------------------------------------| | back | Go to the previous menu. | | exit | Exit w3af. | |-------------------------------------------------| w3af/config:target>>> view #显示目标信息 |------------------------------------------------| | Setting | Value | Modified | Description | |------------------------------------------------| | target_framework | unknown | | Target programming framework (unknown/php/asp/asp.net/java/jsp/cfm/ruby/perl) | | target | | | A comma separated list of URLs | | target_os | unknown | | Target operating system (unknown/unix/windows) | |------------------------------------------------| w3af>>> http-settings #http设定 w3af/config:http-settings>>> help |-------------------------------------------------| | view | List the available options and their values. | | set | Set a parameter value. | | save | Save the configured settings. | |-------------------------------------------------| | back | Go to the previous menu. | | exit | Exit w3af. | |-------------------------------------------------| w3af/config:http-settings>>> view |-------------------------------------------------| | Setting | Value | Modified | Description | |-------------------------------------------------| | url_parameter | | | Append the given URL parameter to every accessed URL. Example: | 。。。。。。 。。。。。。 | basic_auth_domain | | | Set the basic authentication domain for HTTP requests | |-------------------------------------------------| w3af>>> misc-settings #软件设定 w3af/config:misc-settings>>> help |-------------------------------------------------| | view | List the available options and their values. | | set | Set a parameter value. | | save | Save the configured settings. | |-------------------------------------------------| | back | Go to the previous menu. | | exit | Exit w3af. | |-------------------------------------------------| w3af/config:misc-settings>>> view |-----------------------------------------------| | Setting | Value | Modified | Description | |-----------------------------------------------| | msf_location | /opt/metasploit3/bin/ | | Full path of Metasploit framework binary directory | 。。。。。。 。。。。。。 | fuzz_cookies | False | | Indicates if w3af plugins will use cookies as a fuzzable parameter | |-----------------------------------------------| w3af>>> exit #退出
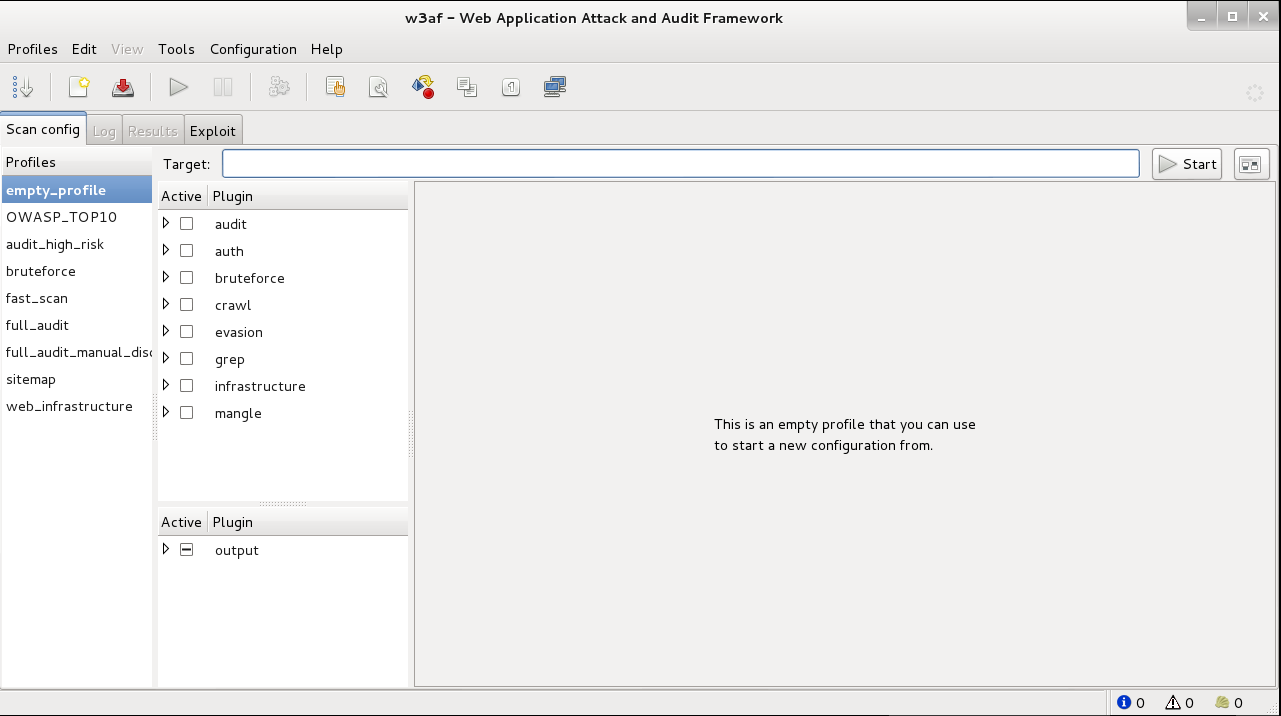
w3af_gui:
如下图,和上面的命令基本对应:
发表评论